IT-Abkürzungsverzeichnis
Ein umfangreiches Verzeichnis für den IT-Bereich
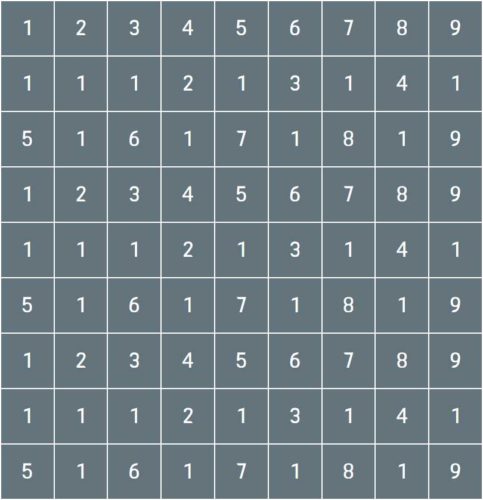
| Abkürzung | Ausschreibung |
|---|---|
| AAA | Authentication Authorization Accounting |
| AAC | Advanced Audio Coding |
| ABAC | Attribute Based Access Control |
| ACL | Access Control List |
| ACLS | Access Control List Services |
| ACME | Automated Certificate Management Environment |
| ACPI | Advanced Configuration and Power Interface |
| AD | Active Directory |
| ADB | Android Debug Bridge |
| ADC | Analog Digital Converter |
| ADF | Application Development Framework |
| ADFS | Active Directory Federation Services |
| AES | Advanced Encryption Standard |
| AFS | Andrew File System |
| AGI | Artificial General Intelligence |
| AI | Artificial Intelligence |
| AIX | Advanced Interactive Executive |
| AJP | Apache JServ Protocol |
| ALPN | Application Layer Protocol Negotiation |
| ALSA | Advanced Linux Sound Architecture |
| AMQP | Advanced Message Queuing Protocol |
| ANN | Artificial Neural Network |
| AOE | ATA over Ethernet |
| AOT | Ahead Of Time |
| API | Application Programming Interface |
| APIPA | Automatic Private IP Addressing |
| APK | Android Package |
| APM | Application Performance Monitoring |
| ARP | Address Resolution Protocol |
| ASAP | As Soon As Possible |
| ASCII | American Standard Code for Information Interchange |
| ASIC | Application Specific Integrated Circuit |
| ASLR | Address Space Layout Randomization |
| ASN | Autonomous System Number |
| ASP | Active Server Pages |
| AST | Abstract Syntax Tree |
| ATM | Asynchronous Transfer Mode |
| AUX | Auxiliary |
| AV | Antivirus |
| AVX | Advanced Vector Extensions |
| B2B | Business To Business |
| B2C | Business To Consumer |
| BACnet | Building Automation and Control Networks |
| BAS | Building Automation System |
| BASH | Bourne Again Shell |
| BCDR | Business Continuity Disaster Recovery |
| BERT | Bidirectional Encoder Representations from Transformers |
| BGP | Border Gateway Protocol |
| BI | Business Intelligence |
| BIND | Berkeley Internet Name Domain |
| BIOS | Basic Input Output System |
| BIT | Binary Digit |
| BLF | Busy Lamp Field |
| BLOB | Binary Large Object |
| BMC | Bare Metal Cloud |
| BOM | Bill Of Materials |
| BOOT | Bootstrap |
| BPS | Bits Per Second |
| BRIDGE | Binary Routing Interface Dynamic Group Engine |
| BSD | Berkeley Software Distribution |
| BSP | Board Support Package |
| BSS | Basic Service Set |
| BSSID | Basic Service Set Identifier |
| BTRFS | B Tree File System |
| BYOD | Bring Your Own Device |
| CAA | Certification Authority Authorization |
| CAAS | Container as a Service |
| CAD | Computer Aided Design |
| CAM | Computer Aided Manufacturing |
| CAPTCHA | Completely Automated Public Turing test to tell Computers and Humans Apart |
| CAS | Central Authentication Service |
| CDFS | Compact Disc File System |
| CDN | Content Delivery Network |
| CEF | Common Event Format |
| CGI | Common Gateway Interface |
| CI | Continuous Integration |
| CIDR | Classless Inter Domain Routing |
| CIFS | Common Internet File System |
| CLF | Common Log Format |
| CLI | Command Line Interface |
| CMOS | Complementary Metal Oxide Semiconductor |
| CNAME | Canonical Name |
| CNI | Container Network Interface |
| COBOL | Common Business Oriented Language |
| COM | Component Object Model |
| CORBA | Common Object Request Broker Architecture |
| CPAN | Comprehensive Perl Archive Network |
| CPE | Customer Premises Equipment |
| CPU | Central Processing Unit |
| CRC | Cyclic Redundancy Check |
| CRON | Command Run On |
| CRUD | Create Read Update Delete |
| CSMA | Carrier Sense Multiple Access |
| CSP | Cloud Service Provider |
| CSS | Cascading Style Sheets |
| CSV | Comma Separated Values |
| CTI | Computer Telephony Integration |
| CUPS | Common Unix Printing System |
| DAC | Digital Analog Converter |
| DAO | Data Access Object |
| DAST | Dynamic Application Security Testing |
| DB | Database |
| DBMS | Database Management System |
| DC | Domain Controller |
| DCIM | Data Center Infrastructure Management |
| DDoS | Distributed Denial Of Service |
| DDR | Double Data Rate |
| DES | Data Encryption Standard |
| DHCP | Dynamic Host Configuration Protocol |
| DIMM | Dual Inline Memory Module |
| DKIM | DomainKeys Identified Mail |
| DLL | Dynamic Link Library |
| DLP | Data Loss Prevention |
| DMARC | Domain Based Message Authentication Reporting and Conformance |
| DMZ | Demilitarized Zone |
| DNS | Domain Name System |
| DoH | DNS over HTTPS |
| DoT | DNS over TLS |
| DPDK | Data Plane Development Kit |
| DRBD | Distributed Replicated Block Device |
| DRM | Digital Rights Management |
| DSCP | Differentiated Services Code Point |
| DSL | Digital Subscriber Line |
| DTMF | Dual Tone Multi Frequency |
| DTO | Data Transfer Object |
| DVCS | Distributed Version Control System |
| DX | Developer Experience |
| EAI | Enterprise Application Integration |
| EAP | Extensible Authentication Protocol |
| eBPF | Extended Berkeley Packet Filter |
| EC2 | Elastic Compute Cloud |
| ECC | Error Correcting Code |
| ECDSA | Elliptic Curve Digital Signature Algorithm |
| ECMAScript | European Computer Manufacturers Association Script |
| EDID | Extended Display Identification Data |
| EDR | Endpoint Detection and Response |
| EFI | Extensible Firmware Interface |
| EFS | Encrypting File System |
| EIGRP | Enhanced Interior Gateway Routing Protocol |
| ELK | Elasticsearch Logstash Kibana |
| EMI | Electromagnetic Interference |
| eMMC | Embedded MultiMediaCard |
| EOF | End Of File |
| EOL | End Of Life |
| EPS | Encapsulated PostScript |
| ERP | Enterprise Resource Planning |
| ESB | Enterprise Service Bus |
| ESD | Electrostatic Discharge |
| eSIM | Embedded Subscriber Identity Module |
| ESR | Extended Support Release |
| ESXi | Elastic Sky X Integrated |
| ETL | Extract Transform Load |
| EULA | End User License Agreement |
| EVPN | Ethernet Virtual Private Network |
| EXIF | Exchangeable Image File Format |
| FaaS | Function as a Service |
| FAT | File Allocation Table |
| FEC | Forward Error Correction |
| FIDO | Fast Identity Online |
| FIFO | First In First Out |
| FIM | File Integrity Monitoring |
| FIPS | Federal Information Processing Standards |
| FLOSS | Free Libre Open Source Software |
| FPGA | Field Programmable Gate Array |
| FPU | Floating Point Unit |
| FQDD | Fully Qualified Device Descriptor |
| FQDN | Fully Qualified Domain Name |
| FRR | Free Range Routing |
| FRU | Field Replaceable Unit |
| FSCK | File System Consistency Check |
| FSM | Finite State Machine |
| FTP | File Transfer Protocol |
| FTPS | File Transfer Protocol Secure |
| FUSE | Filesystem in Userspace |
| FUSE3 | Filesystem in Userspace Version 3 |
| GA | General Availability |
| Gbit | Gigabit |
| GCC | GNU Compiler Collection |
| GCD | Greatest Common Divisor |
| GCM | Galois Counter Mode |
| GDB | GNU Debugger |
| GDI | Graphics Device Interface |
| GEANT | Groupe Europeen de Recherche et de Developpement en Informatique |
| GIF | Graphics Interchange Format |
| GIMP | GNU Image Manipulation Program |
| GKE | Google Kubernetes Engine |
| GPG | GNU Privacy Guard |
| GPIO | General Purpose Input Output |
| GPO | Group Policy Object |
| GPT | GUID Partition Table |
| GPU | Graphics Processing Unit |
| GRE | Generic Routing Encapsulation |
| GRPC | Google Remote Procedure Call |
| GSM | Global System for Mobile Communications |
| GSuite | Google Suite |
| GTM | Google Tag Manager |
| GUI | Graphical User Interface |
| GUID | Globally Unique Identifier |
| GZIP | GNU Zip |
| H.264 | High Efficiency Video Coding |
| H.265 | High Efficiency Video Coding |
| HA | High Availability |
| HBA | Host Bus Adapter |
| HBAA | Host Based Access Authentication |
| HCI | Human Computer Interaction |
| HCL | HashiCorp Configuration Language |
| HDD | Hard Disk Drive |
| HDDI | High Data Density Interface |
| HDMI | High Definition Multimedia Interface |
| HEVC | High Efficiency Video Coding |
| HIDS | Host Intrusion Detection System |
| HIPAA | Health Insurance Portability and Accountability Act |
| HLS | HTTP Live Streaming |
| HMAC | Hash Based Message Authentication Code |
| HMI | Human Machine Interface |
| HSM | Hardware Security Module |
| HSTS | HTTP Strict Transport Security |
| HTA | HTML Application |
| HTCPCP | Hyper Text Coffee Pot Control Protocol |
| HTML | HyperText Markup Language |
| HTTP | HyperText Transfer Protocol |
| HTTP2 | HyperText Transfer Protocol Version 2 |
| HTTP3 | HyperText Transfer Protocol Version 3 |
| HTTPS | HyperText Transfer Protocol Secure |
| HUD | Heads Up Display |
| HVM | Hardware Virtual Machine |
| IaaS | Infrastructure as a Service |
| IaC | Infrastructure as Code |
| IANA | Internet Assigned Numbers Authority |
| IBAN | International Bank Account Number |
| IBGP | Internal Border Gateway Protocol |
| IBSS | Independent Basic Service Set |
| ICA | Independent Computing Architecture |
| ICANN | Internet Corporation for Assigned Names and Numbers |
| ICMP | Internet Control Message Protocol |
| ICS | Industrial Control Systems |
| IDE | Integrated Development Environment |
| IDEA | International Data Encryption Algorithm |
| IDN | Internationalized Domain Name |
| IDP | Identity Provider |
| IDS | Intrusion Detection System |
| IEEE | Institute of Electrical and Electronics Engineers |
| IETF | Internet Engineering Task Force |
| IGMP | Internet Group Management Protocol |
| IKE | Internet Key Exchange |
| IMAP | Internet Message Access Protocol |
| IMSI | International Mobile Subscriber Identity |
| IOPS | Input Output Operations Per Second |
| IoT | Internet of Things |
| IP | Internet Protocol |
| IPAM | IP Address Management |
| IPMI | Intelligent Platform Management Interface |
| IPS | Intrusion Prevention System |
| IPsec | Internet Protocol Security |
| IRQ | Interrupt Request |
| ISAKMP | Internet Security Association and Key Management Protocol |
| iSCSI | Internet Small Computer Systems Interface |
| ISDN | Integrated Services Digital Network |
| ISO | International Organization for Standardization |
| ISP | Internet Service Provider |
| IST | Information Security Team |
| ITIL | Information Technology Infrastructure Library |
| IVR | Interactive Voice Response |
| IX | Internet Exchange |
| JAR | Java Archive |
| JAX | RS – Java API for RESTful Web Services |
| JCE | Java Cryptography Extension |
| JCL | Job Control Language |
| JDBC | Java Database Connectivity |
| JDK | Java Development Kit |
| JIT | Just In Time |
| JMX | Java Management Extensions |
| JNA | Java Native Access |
| JNI | Java Native Interface |
| JPA | Java Persistence API |
| JPEG | Joint Photographic Experts Group |
| JRE | Java Runtime Environment |
| JSF | JavaServer Faces |
| JSON | JavaScript Object Notation |
| JSP | JavaServer Pages |
| JTA | Java Transaction API |
| JWT | JSON Web Token |
| K8s | Kubernetes |
| KAFKA | Apache Kafka |
| KB | Kilobyte |
| KDC | Key Distribution Center |
| KDE | K Desktop Environment |
| KDF | Key Derivation Function |
| KEX | Key Exchange |
| KMS | Key Management Service |
| KNN | K Nearest Neighbors |
| KOPS | Kubernetes Operations |
| KPI | Key Performance Indicator |
| KPT | Kubernetes Packaging Tool |
| KRACK | Key Reinstallation Attack |
| KSM | Kernel Samepage Merging |
| KVM | Kernel Virtual Machine |
| L2TP | Layer 2 Tunneling Protocol |
| LACP | Link Aggregation Control Protocol |
| LAMP | Linux Apache MySQL PHP |
| LAN | Local Area Network |
| LB | Load Balancer |
| LCM | Lifecycle Management |
| LDAP | Lightweight Directory Access Protocol |
| LDAPS | Lightweight Directory Access Protocol Secure |
| LED | Light Emitting Diode |
| LESS | Linux Environment Switching System |
| LF | Line Feed |
| LIFO | Last In First Out |
| LKM | Loadable Kernel Module |
| LLDP | Link Layer Discovery Protocol |
| LMS | Learning Management System |
| LNB | Low Noise Block |
| LOC | Lines Of Code |
| LPAR | Logical Partition |
| LPI | Linux Professional Institute |
| LSB | Least Significant Bit |
| LTS | Long Term Support |
| LVM | Logical Volume Manager |
| LXC | Linux Containers |
| LXCFS | Linux Container File System |
| LXD | Linux Container Daemon |
| MAAS | Metal as a Service |
| MAC | Media Access Control |
| MAM | Mobile Application Management |
| MAN | Metropolitan Area Network |
| MAP | Message Access Protocol |
| MBaaS | Mobile Backend as a Service |
| MBR | Master Boot Record |
| MD5 | Message Digest 5 |
| MDC | Mobile Data Collection |
| MDM | Mobile Device Management |
| MEC | Multi Access Edge Computing |
| MES | Manufacturing Execution System |
| MFA | Multi Factor Authentication |
| MFT | Managed File Transfer |
| MIB | Management Information Base |
| MIDI | Musical Instrument Digital Interface |
| MIME | Multipurpose Internet Mail Extensions |
| MITM | Man In The Middle |
| ML | Machine Learning |
| MLOps | Machine Learning Operations |
| MMC | Microsoft Management Console |
| MMU | Memory Management Unit |
| MOTD | Message Of The Day |
| MP3 | MPEG Audio Layer III |
| MPEG | Moving Picture Experts Group |
| MPLS | Multiprotocol Label Switching |
| MPS | Managed Print Services |
| MQTT | Message Queuing Telemetry Transport |
| MSA | Microservices Architecture |
| MSB | Most Significant Bit |
| MSI | Microsoft Installer |
| MTU | Maximum Transmission Unit |
| MUA | Mail User Agent |
| MVC | Model View Controller |
| MWI | Message Waiting Indicator |
| NAC | Network Access Control |
| NAS | Network Attached Storage |
| NAT | Network Address Translation |
| NAT64 | Network Address Translation IPv6 to IPv4 |
| NB | IoT – Narrowband Internet of Things |
| NDA | Non Disclosure Agreement |
| NDP | Neighbor Discovery Protocol |
| NETCONF | Network Configuration Protocol |
| NFS | Network File System |
| NFV | Network Functions Virtualization |
| NGFW | Next Generation Firewall |
| NGINX | Engine X |
| NIC | Network Interface Card |
| NIDS | Network Intrusion Detection System |
| NLA | Network Level Authentication |
| NMCLI | Network Manager Command Line Interface |
| NOC | Network Operations Center |
| NSX | Network Virtualization Platform |
| NTP | Network Time Protocol |
| NVMe | Non Volatile Memory Express |
| OAUTH | Open Authorization |
| OAUTHA | OAuth Authentication |
| OCR | Optical Character Recognition |
| OCSP | Online Certificate Status Protocol |
| ODBC | Open Database Connectivity |
| OID | Object Identifier |
| OLAP | Online Analytical Processing |
| ONVIF | Open Network Video Interface Forum |
| OOM | Out Of Memory |
| OPC | Open Platform Communications |
| OPNsense | Open Source Firewall Platform |
| OS | Operating System |
| OSI | Open Systems Interconnection |
| OSPF | Open Shortest Path First |
| OTP | One Time Password |
| OVF | Open Virtualization Format |
| P2P | Peer To Peer |
| PaaS | Platform as a Service |
| PAM | Pluggable Authentication Modules |
| PAN | Personal Area Network |
| PAP | Password Authentication Protocol |
| PAT | Port Address Translation |
| PBKDF | Password Based Key Derivation Function |
| PBX | Private Branch Exchange |
| PCI | Peripheral Component Interconnect |
| PCIe | Peripheral Component Interconnect Express |
| Portable Document Format | |
| PDU | Power Distribution Unit |
| PFS | Perfect Forward Secrecy |
| PHP | Hypertext Preprocessor |
| PHY | Physical Layer |
| PIM | Protocol Independent Multicast |
| PKI | Public Key Infrastructure |
| PLC | Programmable Logic Controller |
| PM2 | Process Manager 2 |
| PNG | Portable Network Graphics |
| PoE | Power over Ethernet |
| POP3 | Post Office Protocol 3 |
| POSIX | Portable Operating System Interface |
| PPP | Point To Point Protocol |
| PPTP | Point To Point Tunneling Protocol |
| PROM | Programmable Read Only Memory |
| Proxy | Proxy Server |
| PWA | Progressive Web App |
| QA | Quality Assurance |
| QAM | Quadrature Amplitude Modulation |
| QEMU | Quick Emulator |
| QKD | Quantum Key Distribution |
| QNX | Quantum Unix |
| QoE | Quality of Experience |
| QoS | Quality of Service |
| QR | Quick Response |
| RADIUS | Remote Authentication Dial In User Service |
| RAID | Redundant Array of Independent Disks |
| RAM | Random Access Memory |
| RASP | Runtime Application Self Protection |
| RBAC | Role Based Access Control |
| RCS | Revision Control System |
| RDP | Remote Desktop Protocol |
| REST | Representational State Transfer |
| RFID | Radio Frequency Identification |
| RHEL | Red Hat Enterprise Linux |
| RIP | Routing Information Protocol |
| ROM | Read Only Memory |
| RPC | Remote Procedure Call |
| RPKI | Resource Public Key Infrastructure |
| RSA | Rivest Shamir Adleman |
| RSYNC | Remote Sync |
| RTCP | Real Time Control Protocol |
| RTOS | Real Time Operating System |
| RTP | Real Time Transport Protocol |
| SaaS | Software as a Service |
| SAML | Security Assertion Markup Language |
| SAN | Storage Area Network |
| SASE | Secure Access Service Edge |
| SBC | Session Border Controller |
| SCAP | Security Content Automation Protocol |
| SCM | Source Code Management |
| SDK | Software Development Kit |
| SDLC | Software Development Life Cycle |
| SDN | Software Defined Networking |
| SELinux | Security Enhanced Linux |
| SFTP | SSH File Transfer Protocol |
| SHA | Secure Hash Algorithm |
| SIEM | Security Information and Event Management |
| SIM | Subscriber Identity Module |
| SIP | Session Initiation Protocol |
| SLA | Service Level Agreement |
| SLO | Service Level Objective |
| SMTP | Simple Mail Transfer Protocol |
| SNMP | Simple Network Management Protocol |
| SOAP | Simple Object Access Protocol |
| SOCKS | Socket Secure |
| SPF | Sender Policy Framework |
| SPI | Serial Peripheral Interface |
| SQL | Structured Query Language |
| SRTP | Secure Real Time Transport Protocol |
| SSD | Solid State Drive |
| SSH | Secure Shell |
| SSL | Secure Sockets Layer |
| SSO | Single Sign On |
| STP | Spanning Tree Protocol |
| SVG | Scalable Vector Graphics |
| TACACS | Terminal Access Controller Access Control System |
| TCAM | Ternary Content Addressable Memory |
| TCO | Total Cost of Ownership |
| TCP | Transmission Control Protocol |
| TDD | Test Driven Development |
| TFTP | Trivial File Transfer Protocol |
| TLD | Top Level Domain |
| TLS | Transport Layer Security |
| TOTP | Time Based One Time Password |
| TPM | Trusted Platform Module |
| TSDB | Time Series Database |
| TTL | Time To Live |
| TTY | Teletypewriter |
| U2F | Universal 2nd Factor |
| UART | Universal Asynchronous Receiver Transmitter |
| UAT | User Acceptance Testing |
| UDDI | Universal Description Discovery and Integration |
| UDP | User Datagram Protocol |
| UEFI | Unified Extensible Firmware Interface |
| UID | User Identifier |
| UMA | User Managed Access |
| UML | Unified Modeling Language |
| UNC | Universal Naming Convention |
| UPS | Uninterruptible Power Supply |
| URI | Uniform Resource Identifier |
| URL | Uniform Resource Locator |
| USB | Universal Serial Bus |
| UUID | Universally Unique Identifier |
| V2V | Vehicle To Vehicle |
| V2X | Vehicle To Everything |
| VDI | Virtual Desktop Infrastructure |
| VHD | Virtual Hard Disk |
| VHDX | Virtual Hard Disk Extended |
| VIRTIO | Virtual I/O |
| VLAN | Virtual Local Area Network |
| VM | Virtual Machine |
| VMDK | Virtual Machine Disk |
| VMM | Virtual Machine Monitor |
| VNC | Virtual Network Computing |
| VNF | Virtual Network Function |
| VoIP | Voice over IP |
| VPC | Virtual Private Cloud |
| VPN | Virtual Private Network |
| VPS | Virtual Private Server |
| VR | Virtual Reality |
| VSS | Volume Shadow Copy Service |
| VXLAN | Virtual Extensible LAN |
| W3C | World Wide Web Consortium |
| WAF | Web Application Firewall |
| WAN | Wide Area Network |
| WASM | WebAssembly |
| WCAG | Web Content Accessibility Guidelines |
| WebDAV | Web Distributed Authoring and Versioning |
| WEP | Wired Equivalent Privacy |
| WINS | Windows Internet Name Service |
| WLAN | Wireless Local Area Network |
| WMI | Windows Management Instrumentation |
| WPA | Wi Fi Protected Access |
| WPS | Wi Fi Protected Setup |
| WSDL | Web Services Description Language |
| WSUS | Windows Server Update Services |
| WWW | World Wide Web |
| X11 | X Window System |
| XDR | Extended Detection and Response |
| XFS | X File System |
| XHTML | Extensible HyperText Markup Language |
| XIP | Execute In Place |
| XML | Extensible Markup Language |
| XMPP | Extensible Messaging and Presence Protocol |
| XMS | Extended Memory Specification |
| XOR | Exclusive OR |
| XSRF | Cross Site Request Forgery |
| YAML | Yet Another Markup Language |
| YANG | Yet Another Next Generation |
| YARN | Yet Another Resource Negotiator |
| YMODEM | YMODEM Protocol |
| ZABBIX | Zabbix Monitoring System |
| ZFS | Zettabyte File System |
| ZIF | Zero Insertion Force |
| ZIGBEE | Zigbee Wireless Protocol |
| ZIP | Zone Improvement Plan |
| ZRAM | Compressed RAM Block Device |
| ZSH | Z Shell |
| ZTP | Zero Touch Provisioning |
| ZVOL | ZFS Volume |
Das IT-Abkürzungsverzeichnis bietet eine übersichtliche Sammlung gängiger und spezieller Abkürzungen aus der Informationstechnologie. In der IT werden täglich Akronyme, Kurzformen und technische Bezeichnungen verwendet, die ohne Kontext schwer verständlich sein können. Dieses Verzeichnis hilft dabei, Abkürzungen schnell einer klaren und eindeutigen Ausschreibung zuzuordnen – unabhängig davon, ob sie aus den Bereichen Netzwerk, Softwareentwicklung, Sicherheit, Cloud, Hardware oder Telekommunikation stammen.
Gerade in komplexen IT-Umgebungen ist es entscheidend, Abkürzungen sicher einordnen zu können, um Missverständnisse zu vermeiden und effizient zu arbeiten. Wer weiß, wofür Begriffe wie Protokolle, Standards oder Systemkomponenten stehen, kann technische Dokumentationen besser verstehen, Gespräche präziser führen und fundierte Entscheidungen treffen. Das IT-Abkürzungsverzeichnis unterstützt dabei, Wissen zu strukturieren und technische Zusammenhänge schneller zu erfassen.
Die alphabetische Struktur und die integrierte Suchfunktion ermöglichen einen schnellen Zugriff auf relevante IT-Abkürzungen und deren vollständige Bedeutungen. Ob für Ausbildung, Studium, berufliche Praxis oder als Nachschlagewerk im Alltag – dieses Verzeichnis dient als zuverlässige Referenz für alle, die regelmäßig mit IT-Begriffen arbeiten und ihre Fachkenntnisse gezielt erweitern möchten.